
Guest blog post by HawkSoft
Cybersecurity is a big topic, so let’s break it down to three areas as they relate to independent insurance agencies:
Understand the threat: Explore the current state of cybersecurity worldwide and the pace and tangible costs of breaches.
Impact on independent agents: Analyze how cybersecurity and breaches impact IAs and use a data breach calculator to estimate how much one can cost your agency.
Protect your agency from hackers: Actions that you can apply today to protect your agency, including a 10-point Cybersecurity Checklist.
Understanding the threat of cyber breaches
2017 was one of the worst years for cyber security in history.
We’re all aware of Equifax breach, but did you know about Deloitte, Verizon, Dow Jones & Company and Gmail?
Most disturbing is that many of the recent large breaches occurred years ago with IT teams only recently discovering or disclosing the damage.
What’s the cost of data breaches?
Leading market analyst Juniper Research estimates that cybercrime will cost businesses more than $2.1 trillion globally by 2019.
This is almost four times the estimated cost of breaches in 2015.
The United States and Canada spent the most to resolve malicious or criminal attacks, with the health care and financial services sectors seeing average costs of $380 and $245 per breached record, according to the 2017 Cost of Data Breach Study.
Hackers and criminal insiders caused 47 percent of all breaches.
What does this mean for independent agents?
Despite cybersecurity concerns, few agencies have implemented security measures.
-
61 percent see a need for an agency cyber liability policy.
-
34 percent have a written security policy.
-
23 percent have a written disaster recovery plan.
Top 4 cybersecurity threats for independent agents
There is no better way to ensure financial devastation in your business than to allow hackers to steal your clients’ and prospects’ sensitive data. IA Magazine compiled these four threats your agency faces right now.
-
 Lone wolf hacker:
Lone wolf hacker:Just being on the internet makes you the wolf’s sheep.
-
Employees: While it's more likely to be someone that has left your company, even trusted current employees can be negligent.A report from Ipswitch states 84 percent of employees use personal email to send sensitive files, and more than 50 percent expose company files or data by uploading to a cloud-based service such as Dropbox.
-
Mobile devices: Insurance agents are heavy telecommuters, making their clients' PII vulnerable when accessing the office network through an unsecured wireless network.
-
Third-party service providers: Your clients’ sensitive data is transferred over the internet to third-party companies, putting it at risk of hackers looking to intercept data.
The small agency myth
Owners of small businesses often say they don’t have the money, time, or infrastructure to invest in cyber liability insurance.
This is one instance where it’s important to avoid being penny wise and pound foolish. Have you considered the cost of not having cyber protection?
"Contrary to popular belief, smaller businesses actually have all the more reason why they should buy the coverage — they don’t have the assets to protect themselves and cover their bottom line.”
Alex Wayne, Executive Vice President, A.J. Wayne & Associates, Inc.
What will a data breach cost my agency?
All states but two (as of this writing) have cyber breach notification laws. Check out Ohio’s data breach notification laws.
You may be at risk of being fined if you don't have a cybersecurity plan.
Using Poneman’s 2017 Cost of Data Breach Study that determined an average cost of $245 per record for financial services companies, it would cost your agency $245,000 if you are hit with a breach to your database (assuming 1,000 affected records/clients).
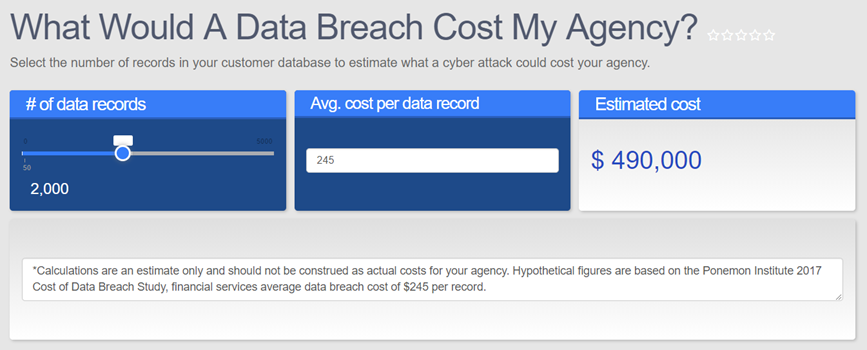 Discover what a data breach might cost your agency by using this calculator.
Discover what a data breach might cost your agency by using this calculator.
How to protect your agency from hackers
Protecting your client’s sensitive information is now one of the most critical responsibilities you face as a modern insurance agent and small business owner.
-
Avoid penalties by complying with federal and state acts
According to Agents Council for Technology (ACT), independent agents could incur substantial penalties for not complying with required regulations of federal and state acts such as Gramm-Leach-Bliley Act ("GLBA"), the New York Department of Financial Services, and other emerging regulatory requirements that protect consumer information. Find out what to do in Ohio.
-
Keep your operating system and antivirus software up-to-date
You still need antivirus protection, but make sure your expectations are realistic about what that software will stop.“The solution," security experts say, "is to deploy technology that keeps a very, very close eye on what's happening inside your network. You can't always prevent attackers from getting in, but you can at least set tripwires to alert you when they do. The survival of your business’s future depends on it.”
-
Secure your email with TLS
ACT recommends use of Transport Layer Security (TLS) to secure electronic transfers of Personal Identifiable Information with carriers.
ACT has created an Agency Cyber Guide you can use in your agency.
It provides resources to comply with 12 cybersecurity regulations, such as a written security policy for you and third-party service providers, staff training and monitoring, encryption and an audit trail.
Take action today: Get started with HawkSoft’s Cybersecurity Checklist
Deploying a comprehensive cybersecurity program takes time and resources.
 The 10-point Cybersecurity Checklist can help start a step-by-step process to implement data security measures.
The 10-point Cybersecurity Checklist can help start a step-by-step process to implement data security measures.
Several items, such as writing a security policy, securing your network and wireless router, and conducting employee training, can be easily implemented to better protect your insurance agency.
The important thing is to start preparing now.
You need to make security compliance a priority. You may be required to do it, and even if you’re not, you can use your preparedness as a competitive advantage when speaking with prospective clients.
NOTE: This is a condensed version of the original article. To read the full article with access to online resources and links, visit hawksoft.com/cybersecurity.






